Welcome back to part two of our FIDO2 blog series! In part one, we explored how to enable FIDO2 key authentication in Microsoft Entra and how to register the key for a user. In this post, we’re diving into the next piece of the puzzle—configuring Windows Hello for Business (WHfB) in Intune to allow FIDO2 key sign-in.
This step is crucial if you want a consistent passwordless experience across your Windows devices, including desktops, laptops, and even mobile (yes, we’ll get to on part 3 of this series!).
Table of Contents:
- Introduction
- Prerequisites
- Enable Windows Hello for Business in Intune
- Enable Windows Passwordless Experience with an Intune device policy
- Testing the new sign in experience on a windows device
- Resetting the Fido Key
- Conclusion
1. Introduction
If you’re planning to roll out FIDO2 keys as a sign-in method, configuring Windows Hello for Business in Intune is essential (especially since this method is more tailored to corporate environments and not something an average user would typically set up in his environment).
Without this method , users can authenticate in browsers or mobile apps but not directly from the Windows lock screen.
Let’s fix that!
2. Prerequisites
Before we start, make sure you meet the following requirements:
Users need an Intune device configuration policy that enables Windows Hello for Business
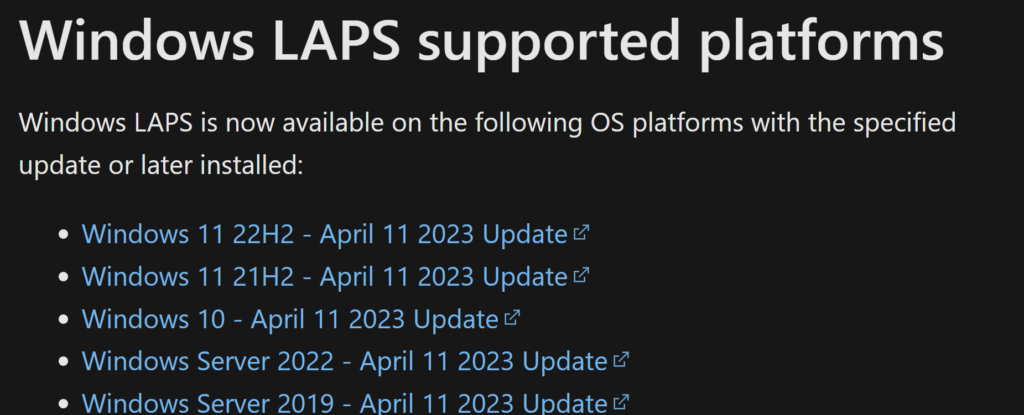
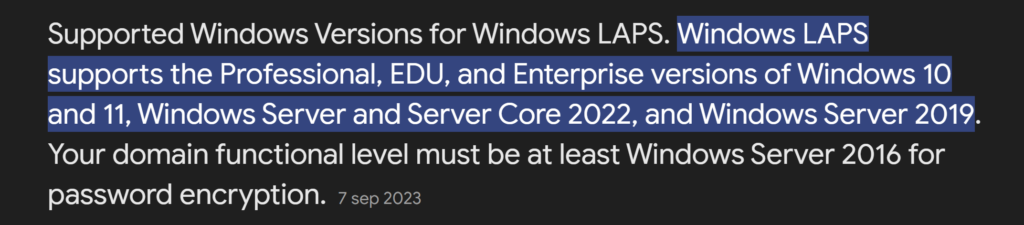
Devices must run Windows 10 version 1903 or later, or Windows 11
Devices should be Azure AD joined (or Hybrid Azure AD joined)
3. Enable Windows Hello for Business in Intune
We want to enable FIDO2 key authentication across all Microsoft systems and for various scenarios. This will allow users to authenticate with the key on a webpage, mobile device, and of course, their personal computer.
Follow the steps below to enable this method within Windows Hello for Business:
- Open the Intune Admin Center and go to Devices.
- Select Enrollment from the menu.
- Choose Windows Hello for Business.
- Enable Windows Hello for Business by toggling it on (if it’s not enabled already).
- Scroll to the bottom and ensure Use security keys for sign-in is enabled.
- Click Save to apply the changes.

If it’s already enabled by your organization, you can skip this step.
4. Enable Windows Passwordless Experience with an Intune device policy
To ensure a full passwordless experience—including Windows Hello for Business sign-in at the lock screen—we also need to configure a policy in Intune.
This setting is needed to make passwordless sign-in work on the Windows lock screen using Windows Hello for Business. Without it, users can still sign in with a FIDO2 key in the browser or on mobile apps, but not directly on the device.
Below are some specific considerations for this part.

And this is how to create the policy in Intune:
Open a browser and go to the Microsoft Intune admin center and follow below steps:
- In the left-hand menu, go to Devices.
- Click on Configuration and then select
- Create to start a new policy.
- For Platform, select Windows 10 and later.
- For Profile type, choose Settings catalog.
- Click Create to continue.

Give the policy a name and continue

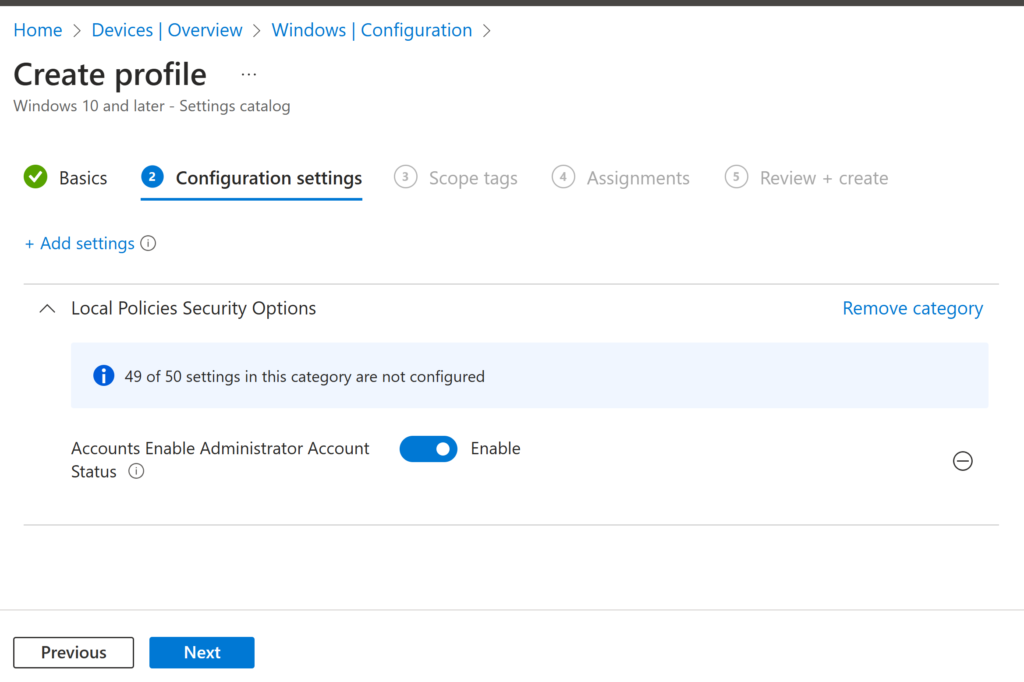
In the next page follow below steps:
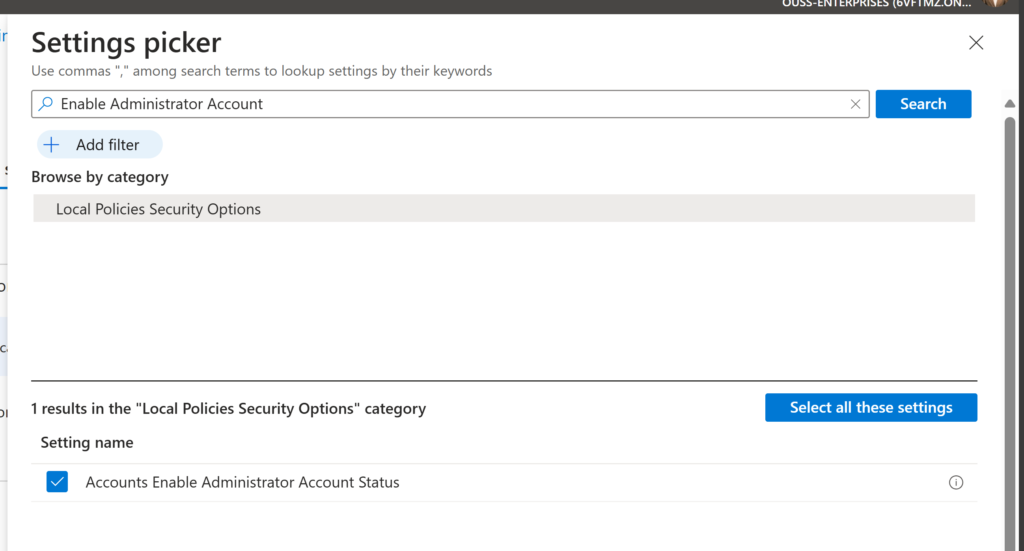
- Click on + Add settings
- In the Settings picker, type “Use security key for sign-in”
- Select Windows Hello for Business
- Under Settings name, select Use security key for sign-in
- Set the option to Enabled

If you make use of scope tags or want to target a specific assignment group (for testing, for example), go ahead and select those. But in our case, we want all Autopilot devices to have this option enabled by default:

If everything looks good, press Next and then Create to enable and deploy the policy.
Once this policy is applied, users will be able to use FIDO2 keys right from the Windows sign-in screen—no password needed. So let’s go ahead and test it out.
5. Testing the new sign in experience on a windows device
In the previous blog, we walked through how to configure and register a FIDO2 key as an authentication method for your user account. If you haven’t done that yet, I recommend checking it out first.
Now that your our FIDO2 key is already set up, let’s test it out for a passwordless Windows sign-in:
Steps to Sign in with Your FIDO2 Key
- On the Windows lock screen, click Other user and click on Sign in options

2. You’ll now see a new option: Sign in with a security key. Insert your FIDO2 key into the USB port and click the option. (Since the key has already been configured, you’ll be prompted to enter your PIN code).
Enter the PIN code you created during setup and press Enter.

3. You will get asked to touch the key when the key’s green Y light flashes, touch the key to continue.

If everything went well you will see the famous Windows Hello logo:

🎉 Congratulations, you’ve just completed your first passwordless login on Windows using a FIDO2 key!
6. Resetting the Fido Key
If you want to change the PIN code or reset the Fido key entirely, download the YubiKey Manager. After the usual next, next, next, the program will launch. Click on Applications, select FIDO2, and choose either Change PIN or Reset FIDO2.
You’ll be prompted to touch the key to verify that it’s in your possession.

7. Conclusion
And that’s it! You’ve now successfully configured Windows Hello for Business to support FIDO2 keys and tested the full sign-in experience—from inserting the key to logging in without typing a password. This is a big step toward a truly passwordless future in your organization and for users to not have to change the password so many times as that’s really something of the past imo.
In the next part of this series, we’ll show you how to use the FIDO2 key for secure Privileged Identity Management (PIM) role activation. That one’s especially important for admins and high-privilege users, so make sure to stick around!
Until next time—stay secure and password-free! 🔐